Insider threats are cybersecurity risks posed by individuals within an organization, such as employees, contractors, or business partners, who have legitimate access to systems and data. These threats can be intentional (malicious actors) or unintentional (negligent individuals) and often result in significant data breaches, financial losses, and reputational damage. Insider threats are particularly challenging because they exploit trusted access, making detection and prevention more complex than external threats.
Insider threats can be broadly categorized into three types:
Malicious Insiders: Employees or associates who intentionally misuse their access to harm the organization. Motivations include financial gain, espionage, or retaliation.
- Example: The Edward Snowden case, where classified NSA data was leaked by a trusted insider.
Negligent Insiders: Individuals who inadvertently compromise security through careless actions, such as clicking on phishing links or mishandling sensitive information.
- Example: An employee sending sensitive files to the wrong recipient.
Compromised Insiders: Employees whose accounts or access credentials are hijacked by external attackers, often through phishing or malware.
- Example: An attacker using stolen employee credentials to access and exfiltrate data.
Impact of Insider Threats
Insider threats have significant consequences:
- Data Breaches: Insider threats account for approximately 34% of all data breaches, according to Verizon’s 2023 Data Breach Investigations Report.
- Financial Losses: The average cost of an insider-related breach is $15.38 million, as reported by the Ponemon Institute’s 2022 Insider Threats Report.
- Reputational Damage: High-profile insider incidents can erode customer trust and impact brand reputation.
- Operational Disruptions: Insider threats can disrupt critical systems, affecting organizational productivity and continuity.
Common Methods of Insider Threats
- Data Exfiltration: Malicious insiders often steal sensitive data using USB drives, cloud storage, or email.
- Privilege Abuse: Insiders misuse elevated permissions to access restricted systems or data.
- Negligent Actions: Mistakes, such as misconfiguring security settings or falling for phishing scams, expose organizations to risks.
- Credential Theft: External attackers leverage stolen credentials to impersonate insiders and exploit their access.
Notable Case Studies
- Edward Snowden (2013): Snowden, an NSA contractor, leaked classified documents detailing global surveillance programs, highlighting the risks of insiders with privileged access.
- Tesla Insider Sabotage (2018): A disgruntled employee at Tesla altered manufacturing software and leaked sensitive data to competitors.
- Capital One Breach (2019): A former employee exploited a misconfigured firewall to access sensitive customer data, affecting over 100 million individuals.
Trends in Insider Threats
- Remote Work Risks: The shift to remote work has increased vulnerabilities, as employees access sensitive systems from less secure environments.
- Ransomware Collaboration: Insiders are increasingly collaborating with ransomware groups, providing access in exchange for financial incentives.
- Use of Dark Web Markets: Insiders sell stolen data or credentials on the dark web, enabling further attacks by external threat actors.
- Advanced Detection Evasion: Malicious insiders use sophisticated techniques to avoid detection, such as hiding their activities within normal workflows.
Mitigation Strategies
- Behavioral Monitoring: Implement tools to track unusual user activity, such as accessing sensitive files at odd hours.
- Least Privilege Principle: Limit access to only what is necessary for an employee’s role, reducing the impact of compromised accounts.
- Employee Training: Educate employees on security best practices to reduce negligence-related risks.
- Regular Audits: Conduct periodic audits of user activity, permissions, and system configurations to identify anomalies.
- Data Loss Prevention (DLP): Use DLP tools to monitor and block unauthorized data transfers.
- Incident Response Plans: Develop and test protocols for responding to insider threats to minimize damage.
Insider threats in government defenses are among the most challenging cybersecurity risks due to their exploitation of legitimate access to classified systems. These threats may arise from malicious insiders seeking to harm national interests, negligent employees whose actions inadvertently expose vulnerabilities, or individuals compromised by external attackers. Such threats often result in intelligence leaks, operational disruptions, financial losses, and reputational damage, making them a critical concern for governments worldwide.
Impact of Insider Threats on Government Defenses
The consequences of insider threats in government operations are severe. Espionage and intelligence leaks, such as the Edward Snowden disclosures, jeopardize ongoing missions and reveal classified programs, endangering national security. Operational disruptions caused by insider sabotage or privilege abuse can impair military readiness or disrupt critical systems. Financial losses related to insider incidents include recovery costs and fines, with reports indicating an average cost of $15 million per incident. Additionally, high-profile insider breaches erode public trust in the government’s ability to safeguard sensitive information and maintain national security.
Methods of Insider Threats
Insider threats manifest in several ways, including data exfiltration, privilege abuse, and sabotage. Malicious insiders often transfer sensitive information through physical or digital means, while negligent employees may misconfigure security settings or fall victim to phishing campaigns. Compromised insiders enable external attackers to exploit their access, often through credential theft or coercion. These methods highlight the complex nature of insider threats, which blend human error with intentional misconduct.
Case Studies
Historical cases emphasize the severity of insider threats in government defenses. Edward Snowden’s unauthorized disclosure of NSA surveillance programs exposed the vulnerabilities of trusted insider access, sparking global debates on privacy and security. Robert Hanssen’s decades-long espionage for Russia severely compromised U.S. defense strategies, and Reality Winner’s leak of intelligence reports highlighted the risks of contractors mishandling classified information. These incidents underscore the critical need for robust insider threat management.
Trends in Insider Threats
Recent trends show an increase in insider threats due to expanded remote work environments, which provide greater access to sensitive systems from less secure locations. Nation-state actors actively exploit insiders to access classified information or disrupt operations. Collaboration between insiders and cybercriminal groups, such as ransomware attackers, adds another layer of complexity. Moreover, insiders increasingly employ sophisticated methods to evade detection, blending malicious actions with normal workflows to remain undetected.
Insider threats pose a significant risk to the financial services sector, given the high value of financial data, proprietary algorithms, and customer trust. Insiders, including employees, contractors, and business partners, can intentionally or unintentionally compromise systems, resulting in financial losses, reputational harm, and regulatory penalties. Due to the sector’s dependence on trust and regulatory compliance, insider threats are particularly impactful and demand robust management strategies.
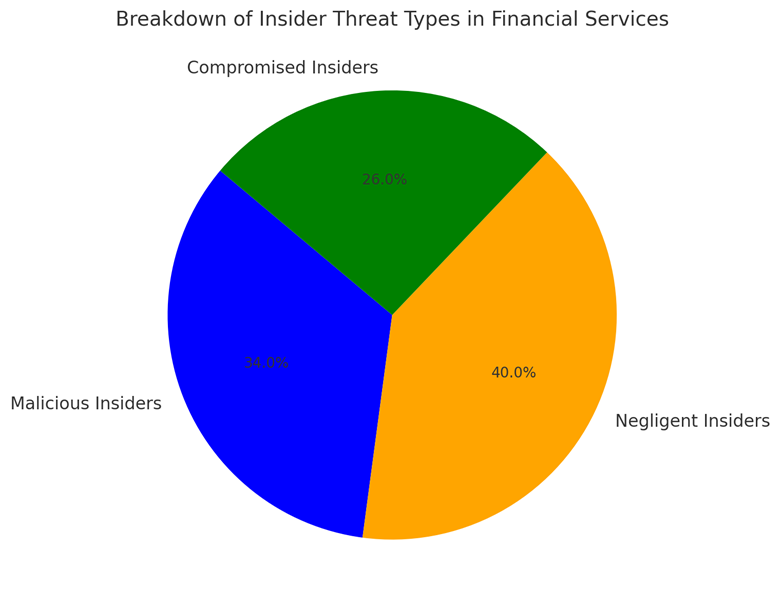
Insider threats in financial services generally fall into three categories. Malicious insiders intentionally exploit their access for personal gain or to harm the organization, such as embezzling funds or leaking sensitive information. Negligent insiders inadvertently expose systems through carelessness, such as mishandling data or falling for phishing scams. Compromised insiders, often victims of social engineering or credential theft, unknowingly facilitate external attacks.
Breakdown of Insider Threat Types in Financial Services
Average Cost of Insider Threat Incidents in Financial Services (in Millions)
The rise in remote work has expanded the attack surface, increasing opportunities for negligence and malicious activity. External cybercriminals increasingly collaborate with insiders, offering financial incentives for access to sensitive systems. Advanced tools and techniques, such as using legitimate workflows to mask malicious activity, make insider threats harder to detect.
Insider threats in financial services account for 28% of all cyber incidents in the sector. The financial impact of these incidents has steadily increased, with the average cost rising from $10.5 million in 2018 to $15.4 million in 2022. These threats lead to data breaches, regulatory fines, and erosion of customer trust, which are critical to the sector’s operations.
Insider threats in healthcare and pharmaceuticals fall into three primary categories:
- Malicious Insiders: These individuals intentionally misuse their access for personal gain, espionage, or sabotage. Examples include stealing intellectual property, such as drug research, for competitive advantage or financial reward.
- Negligent Insiders: Employees or contractors whose careless actions, such as mishandling electronic health records (EHRs) or falling for phishing scams, expose systems to breaches.
- Compromised Insiders: Staff members whose credentials are stolen through phishing or malware, allowing external actors to exploit their access.
Insider threats in this sector lead to a range of severe consequences:
- Data Breaches: Insider threats account for 25% of healthcare data breaches, according to Verizon’s 2023 Data Breach Investigations Report. These breaches compromise protected health information (PHI), leading to regulatory penalties under laws such as HIPAA.
- Intellectual Property Theft: In the pharmaceutical industry, malicious insiders may steal research data related to drug development, causing billions in potential losses and impacting competitive positioning.
- Operational Disruptions: Insider threats can disable critical systems, such as electronic medical record platforms, delaying patient care.
- Regulatory and Financial Costs: Insider-related breaches in healthcare cost an average of $11 million per incident, as reported by the Ponemon Institute’s 2022 study on healthcare data breaches.
Insider threats in healthcare and pharmaceuticals use various methods, including data exfiltration, privilege abuse, and unintentional exposure. Malicious insiders often export sensitive data via unauthorized devices or email accounts. Negligent insiders may leave devices unsecured or fail to follow proper data protection protocols. Compromised insiders often fall victim to phishing attacks, inadvertently giving attackers access to sensitive systems.
Insider threats in critical infrastructure pose significant risks to national security, public safety, and economic stability. Critical infrastructure encompasses sectors such as energy, water, transportation, telecommunications, and healthcare, all of which are essential for societal functioning. Insiders—whether malicious, negligent, or compromised—can exploit their access to disrupt operations, steal sensitive information, or cause physical damage. Due to the critical nature of these systems, insider threats require heightened attention and mitigation efforts.
Insider threats in critical infrastructure generally fall into three categories:
- Malicious Insiders: Individuals who intentionally exploit their access to harm the organization or advance personal or political goals. Examples include sabotaging industrial control systems (ICS) or leaking proprietary information.
- Negligent Insiders: Employees or contractors whose careless actions, such as misconfiguring systems or falling for phishing attacks, inadvertently expose infrastructure to risks.
- Compromised Insiders: Individuals whose credentials are stolen or coerced by external actors to gain unauthorized access to critical systems.
Impact of Insider Threats on Critical Infrastructure
Insider threats have far-reaching consequences for critical infrastructure:
Operational Disruptions: Insiders can disable systems, disrupt supply chains, or shut down essential services, such as power grids or water treatment facilities.
- Example: A former employee of a Kansas water treatment plant intentionally accessed systems remotely in 2019, changing critical operational settings and endangering public safety.
Physical Damage: Insider actions, such as altering ICS configurations, can cause equipment malfunctions, leading to costly repairs or hazardous conditions.
- Example: The 2008 San Francisco Municipal Transportation Agency case, where a disgruntled employee locked administrators out of the system, demonstrating the risks of privilege abuse.
Espionage and Data Theft: Insiders may steal sensitive data, such as operational blueprints or cybersecurity plans, for competitive or geopolitical advantage.
- Example: Nation-state actors recruiting insiders to access sensitive energy or transportation data for strategic gain.
Financial and Reputational Damage: Insider incidents can result in regulatory fines, legal costs, and loss of public trust, further exacerbating the harm to critical infrastructure operators.
