Summary
Cyber threats like malware and ransomware have become pervasive, targeting individuals, businesses, and governments. Understanding the nature of these attacks and the role of cyber threat intelligence (CTI) is essential for mitigating risks. Malware refers to malicious software designed to harm or exploit systems, while ransomware specifically targets a victim’s data by encrypting it and demanding ransom.
Types of Malware
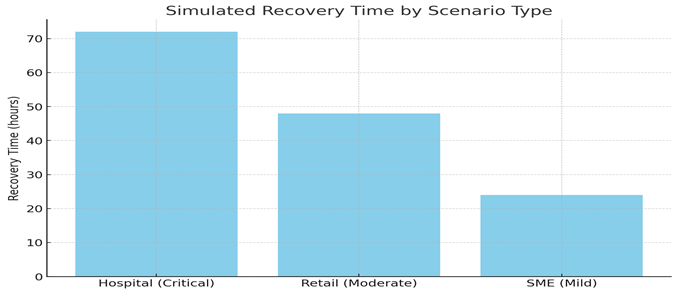
Malware includes several different categories:
- Viruses: Infect programs and replicate when those programs are run.
- Worms: Self-replicating malware that spreads across networks without user intervention.
- Trojans: Disguise themselves as legitimate software, delivering hidden malicious payloads.
- Spyware/Adware: Collects information without user consent or displays unwanted ads.
The following chart illustrates the distribution of common malware types:
Ransomware
Ransomware is a specific type of malware designed to encrypt files and demand a ransom for their release. In many cases, the threat actors may also threaten to expose sensitive data unless the ransom is paid, a tactic known as double extortion.
Common Attack Vectors:
- Phishing Emails: Attachments or links in emails are used to deploy ransomware.
- Exploiting Software Vulnerabilities: Outdated or unpatched systems are common entry points.
- Remote Desktop Protocol (RDP): Poorly configured RDP settings allow attackers to gain access to systems.
Key Example:
- WannaCry (2017): Used an exploit in Windows to infect thousands of computers globally, including healthcare systems.
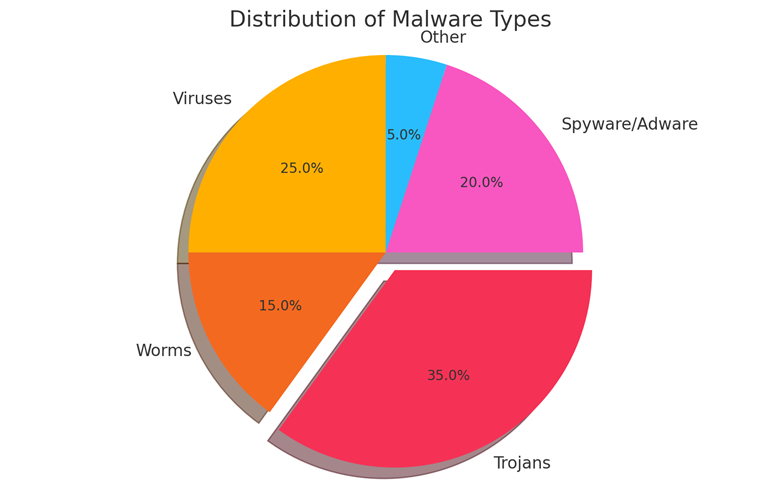
Ransom Payments Over Time
The following chart demonstrates the increasing financial impact of ransomware attacks from 2017 to 2021, with ransom payments increasing from $5 billion to $20 billion:
Role of Cyber Threat Intelligence (CTI)
CTI is essential for detecting, analyzing, and mitigating malware and ransomware threats. CTI focuses on:
- Indicators of Compromise (IOCs): Data like malicious file hashes and IP addresses.
- Tactics, Techniques, and Procedures (TTPs): Understanding the specific actions attackers take.
- Threat Actor Profiles: Understanding the groups behind the attacks (e.g., cybercrime syndicates).
Malware and ransomware are significant threats in the cybersecurity landscape, and a strong understanding of these threats, combined with effective CTI, can help organizations minimize the risk of an attack. Regular backups, patch management, and strong detection mechanisms are crucial for defense.
Psychological & Behavioral Analysis of Malware and Ransomware Attacks
Malware and ransomware attacks are not just technical issues; they also involve complex psychological and behavioral components. Understanding the psychological drivers behind these attacks, both from the attacker and victim perspective, can provide valuable insights for cyber defense strategies and enhance awareness in handling such threats.
Psychology of Attackers
Attackers use malware and ransomware for various reasons, employing psychological tactics to manipulate victims. Key factors influencing their behavior include:
- Financial Motivation (Greed):
Ransomware attackers are often driven by the potential for large financial gains. Cryptocurrency (e.g., Bitcoin) makes it easier for attackers to demand anonymous payments.
- Power and Control:
Attackers gain satisfaction from the control they exert over victims by encrypting files and crippling systems.
- Psychological Manipulation (Social Engineering):
Attackers often exploit human emotions like fear or urgency through phishing emails to trick victims into downloading malware or providing sensitive information.
- Gamification:
Some attackers, particularly younger ones, treat hacking as a game or competition, seeking recognition in underground forums by successfully deploying malware or ransomware.
Psychological Impact on Victims
The psychological effects of malware and ransomware on victims often drive their decision-making during an attack:
- Fear and Panic:
Victims fear losing access to important data, causing them to panic and sometimes make hasty decisions, such as paying the ransom.
- Urgency:
Ransomware attackers impose tight deadlines, which creates psychological pressure and makes victims feel they have no choice but to comply.
- Shame and Guilt:
Victims, especially those in charge of cybersecurity, often feel guilty for allowing the attack, even if it was due to a simple mistake like clicking a phishing link.
- Helplessness:
Many victims feel powerless in the face of ransomware, especially when they lack the technical skills to recover their data without paying the ransom.
- Post-Attack Trauma:
The psychological toll of these attacks can last long after the event, leading to stress, anxiety, and fear of future attacks.
Behavioral Aspects in Defense
Understanding how people behave in response to malware and ransomware attacks can improve defense strategies:
- Security Awareness Training:
Training employees to recognize the psychological tricks (e.g., urgency, fear) that attackers use can reduce the chances of falling victim to phishing or social engineering.
- Incident Response Planning:
Having a clear plan for responding to ransomware attacks reduces panic, as everyone knows what steps to take.
- Behavioral Monitoring:
Monitoring for unusual behaviors, such as accessing unfamiliar files or running unknown processes, can help detect malware early.
Psychological Models in Cyber Threat Intelligence (CTI)
Incorporating psychological and behavioral models into CTI can improve the effectiveness of cybersecurity:
- Motivational Models:
Understanding attacker motivations (financial gain, political motives, etc.) helps predict which targets might be next.
- Risk Perception Models:
These models assess how different individuals and organizations perceive the risk of cyberattacks. Some underestimate the risk, while others overreact, leading to unnecessary stress.
- Trust and Deception Models:
These models examine how attackers build fake trust, for example through phishing emails. Understanding these patterns helps build better security defenses.
Malware and ransomware attacks rely heavily on psychological manipulation, both from the attacker’s side (to exploit human vulnerabilities) and the victim’s side (leading to decisions like paying the ransom). Recognizing these psychological and behavioral factors can help organizations better prepare for, respond to, and prevent these attacks.
Geopolitical and Cultural Insights into Malware and Ransomware Attacks
Malware and ransomware attacks are deeply influenced by geopolitical and cultural factors. Different regions and countries contribute to the development and spread of these cyber threats, driven by various economic, political, and cultural motives. Understanding these influences can help organizations and governments better anticipate, prevent, and respond to cyberattacks.
- Nation-State Sponsored Cyberattacks:
Many ransomware and malware attacks are linked to nation-states. Countries like Russia, China, and North Korea are often implicated in cyberattacks for espionage, sabotage, or financial gain.
Example: Russia has been accused of enabling ransomware groups like REvil, while North Korea’s Lazarus Group used ransomware in the WannaCry attack to generate funds.
- Cybercrime Safe Havens:
Countries with weak cybersecurity laws or poor enforcement provide safe environments for cybercriminals. In regions like Russia and Eastern Europe, attackers operate with little fear of legal consequences, as long as they don’t target local interests.
- Economic Sanctions and Cyber Warfare:
Countries under sanctions, such as North Korea and Iran, often use ransomware and cyberattacks to generate revenue and evade financial restrictions. Cyber warfare is also used as a tool to disrupt and weaken adversaries.
- Cyber Warfare as a Political Tool:
Ransomware attacks can be used as part of hybrid warfare, blending physical military actions with digital attacks. During the Russia-Ukraine conflict, both countries reportedly used cyberattacks, including ransomware, to disrupt each other’s infrastructure.
Cultural Factors in Malware and Ransomware Attacks
- Cybercriminal Subcultures:
In some regions, cybercrime is seen as a lucrative alternative to legitimate employment. Countries like Russia and Eastern Europe have hacker communities that often view attacks on Western targets as acceptable, aligning with anti-Western sentiments.
- Cultural Attitudes Toward Law Enforcement:
Different countries enforce cybersecurity laws with varying levels of strictness. In places like China and Russia, cybercriminals face little punishment as long as they don’t target domestic entities. In contrast, Western countries enforce strict laws and work together on global investigations.
- Localized Targeting:
Cybercriminals often exploit regional knowledge and cultural norms to improve their chances of success. For example, ransomware attacks may increase during Western holidays when organizations have lower staff levels, and phishing emails are tailored in local languages to appear legitimate.
- Cultural Views on Ransomware Payments:
Regions have different attitudes toward paying ransom demands. For instance, Western countries generally advise against paying ransoms, but businesses often do so to restore services. In Asia, particularly Japan and South Korea, companies may pay ransoms more quietly to avoid reputational damage.
Risk Simulation in Malware and Ransomware Attacks
Risk simulation helps organizations understand how malware and ransomware could impact them. Key aspects include:
- Attack Surface Simulation:
Identifies vulnerable points in the network, such as unpatched software or phishing entry points.
- Business Impact Analysis:
Simulates the potential financial and operational impact, allowing organizations to estimate costs related to downtime, ransom payments, and reputational damage.
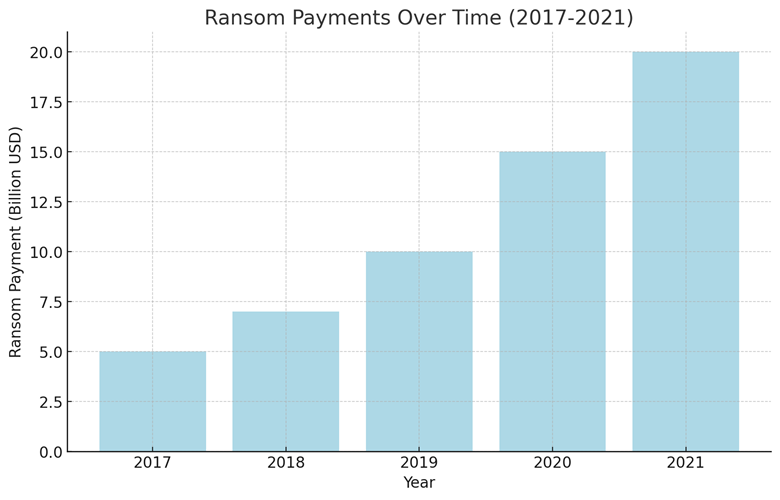
- Recovery Time Simulation:
Predicts how long it would take to recover after a ransomware or malware attack, helping organizations prepare for possible operational disruptions.